In this Solution Guide we pick up where we left off after Arc Onboarding our on prem devices.
Once we have our Connected Machine Agents deployed and we can see our devices are listed in Azure, we can start to focus on the patching options available to them.
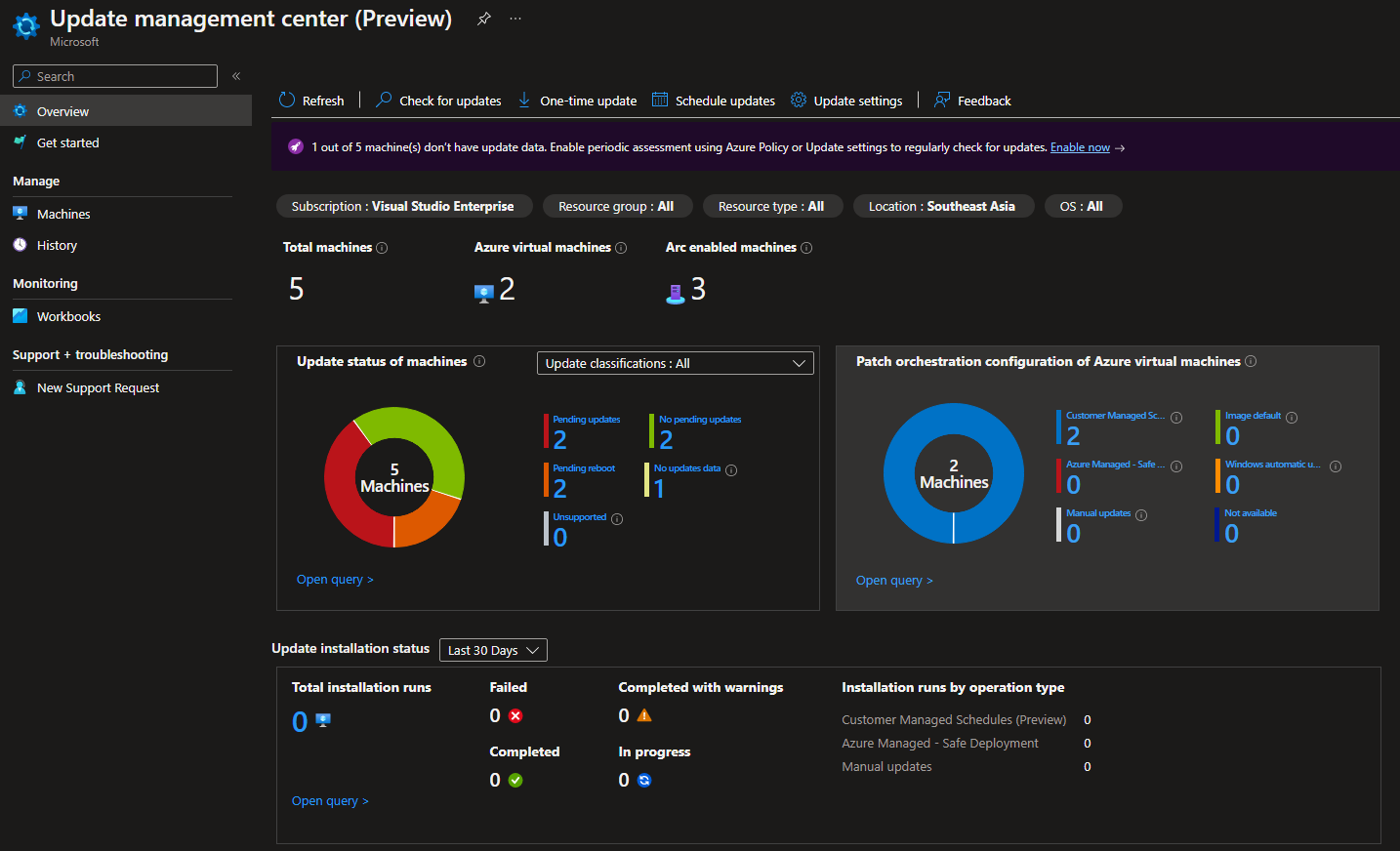
Start by navigating to the Update Management Center, which is still in Preview at the time of writing:
Azure Update Management Center Portal
As you can see below we can view all of the Azure and Azure Arc servers listed within our subscription.
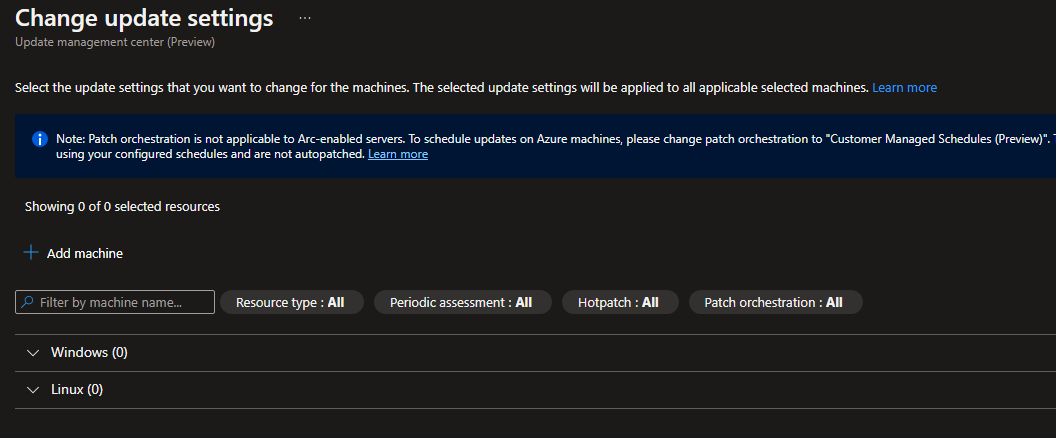
Lets start by configuring the Update Settings targeting our Azure Arc devices, by selecting Update Settings in the top pane.
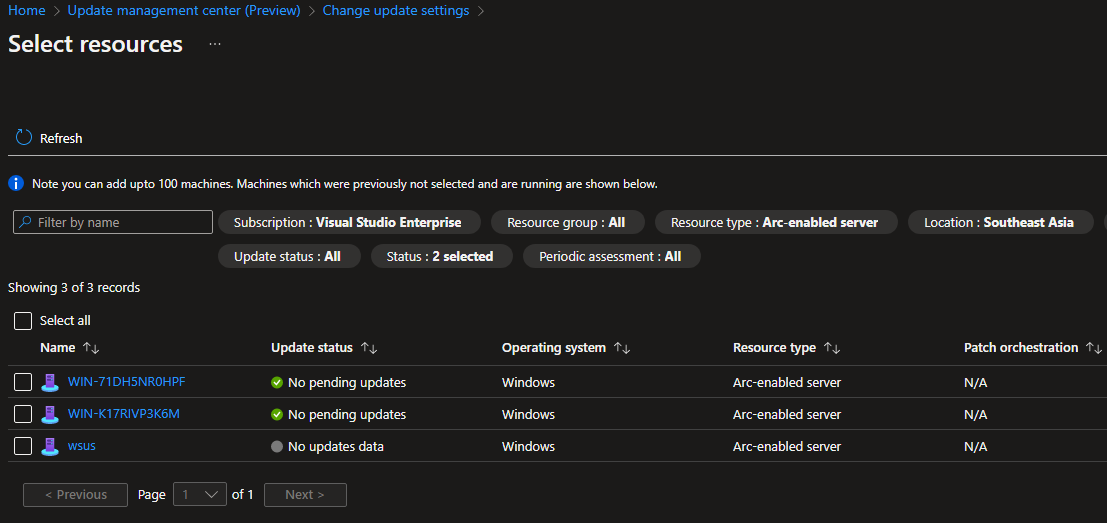
Start by clicking on the + Add Machine button and then filter your results to only list the Azure Arc devices previously onboarded.
Select the devices you wish to target and click next.
Next we can edit the Update Settings for all the selected devices. Start by editing the Periodic Assessment tab to Enable selected devices and click save.
Also note that Patch Orchestration is not available for Azure Arc devices.
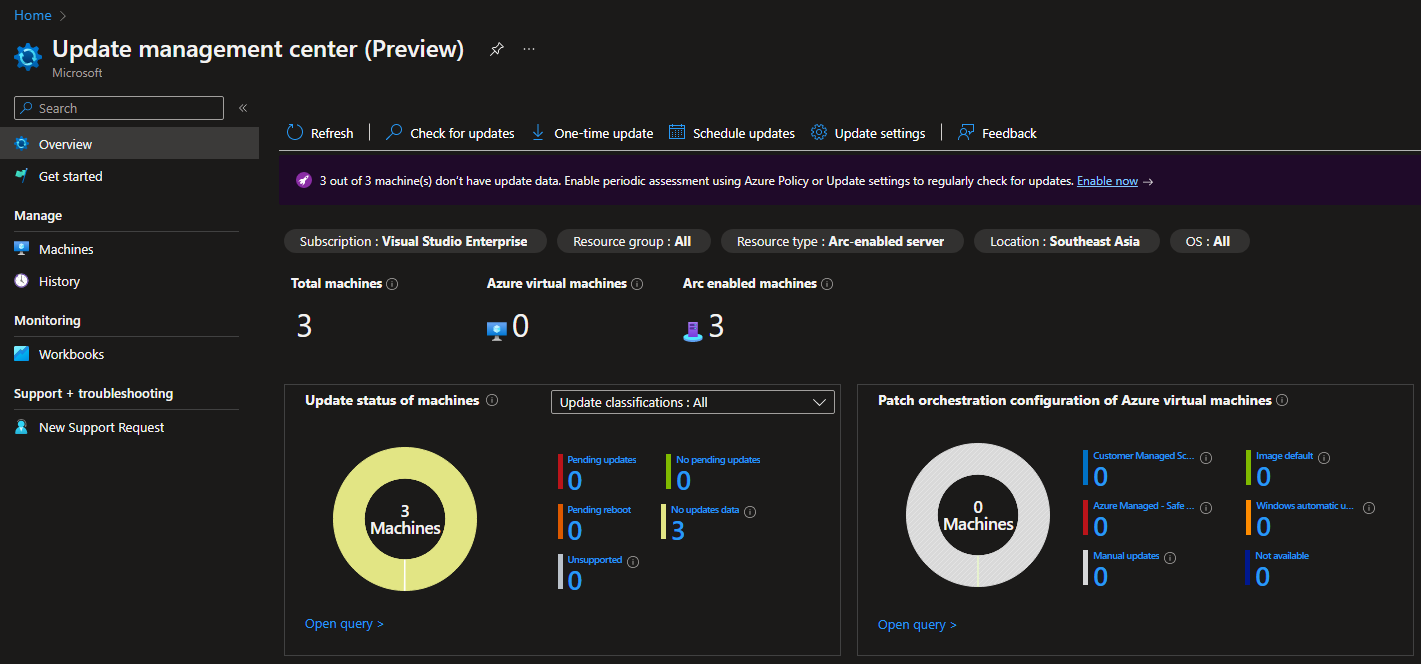
This is great but wouldn’t it be much more efficient if we could automatically enable regular assessment of missing updates for existing and newly onboarded Azure Arc devices?
In walks Azure Policy!
You can now navigate to Azure policy or click the Enable Now from the purple ribbon as shown below:
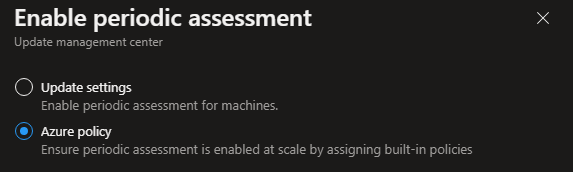
In the popup window select a once off update or select Azure Policy to put a policy in place for all future onboarded devices:
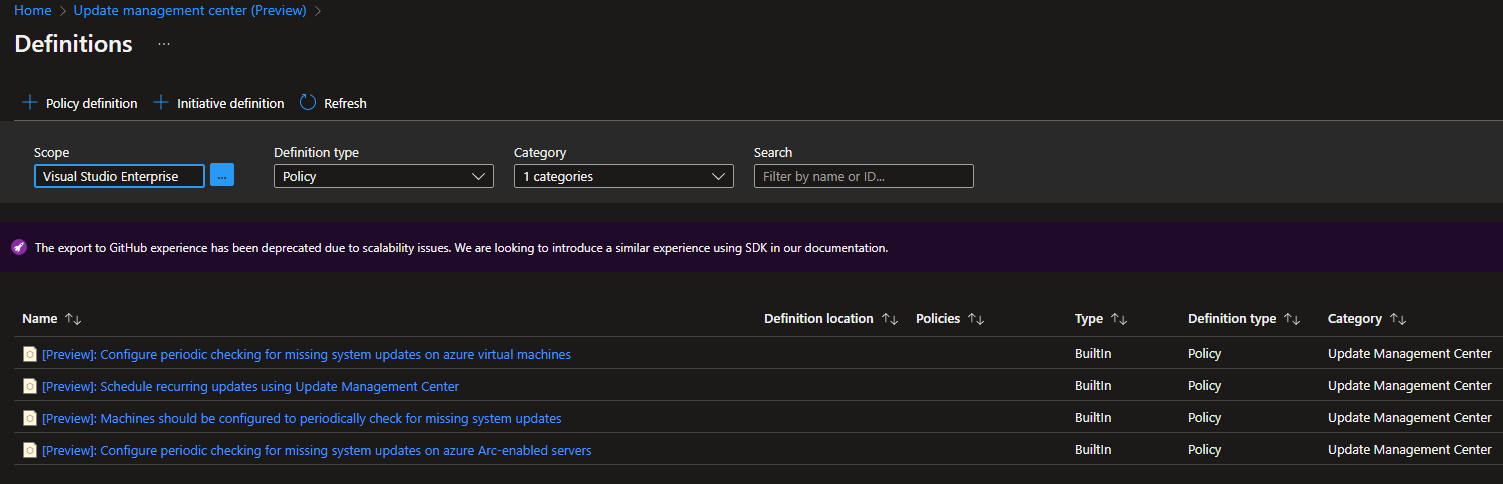
You will be navigated to the Azure policy screen,
Select the [Preview]: Configure periodic checking for missing system updates on azure Arc-enabled Servers option:
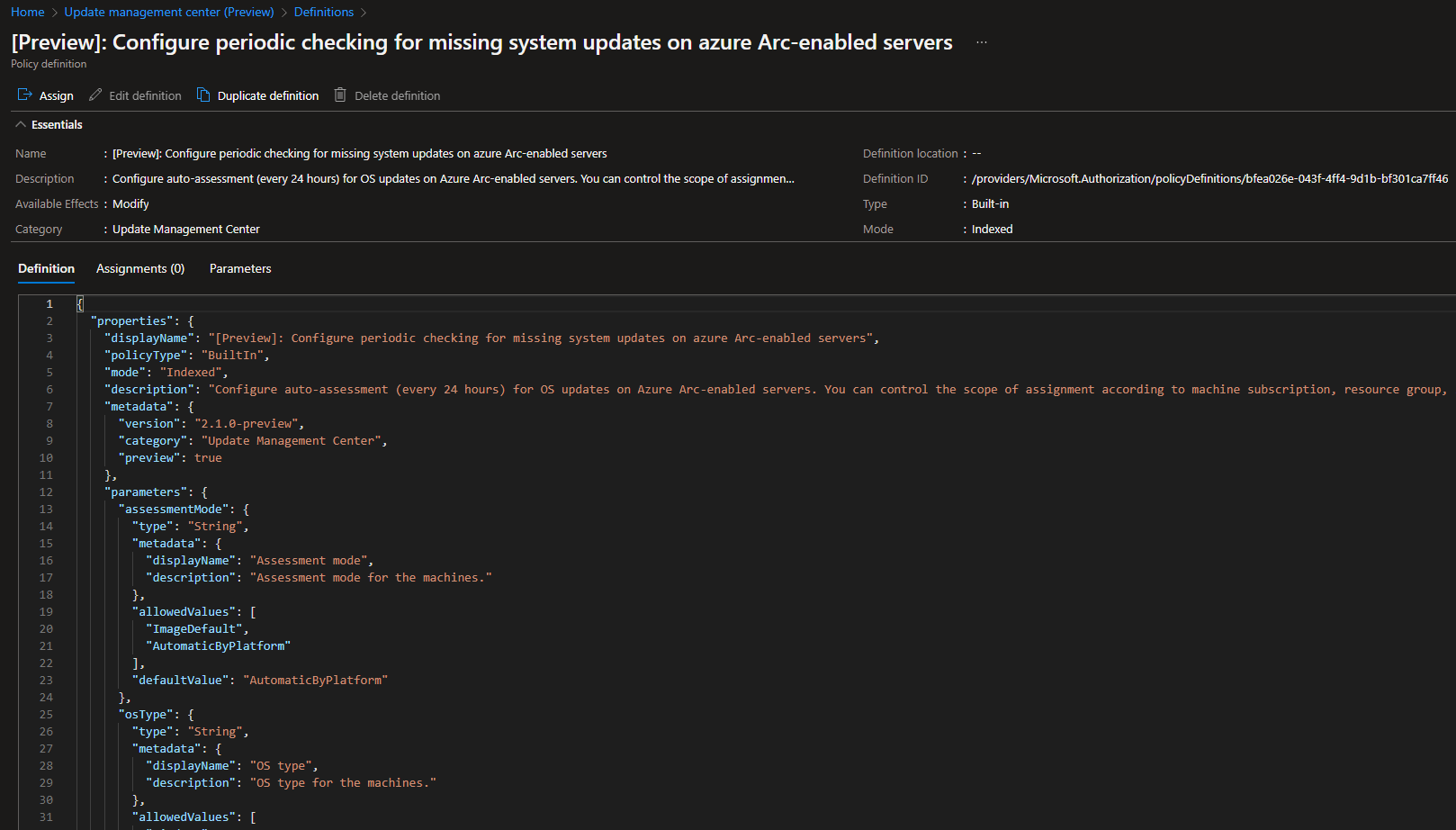
With that the Definition Policy window will appear, here you can drill down to the policy definition to see how the policy is applied.
Once you are happy with the details, click on the Assign button:
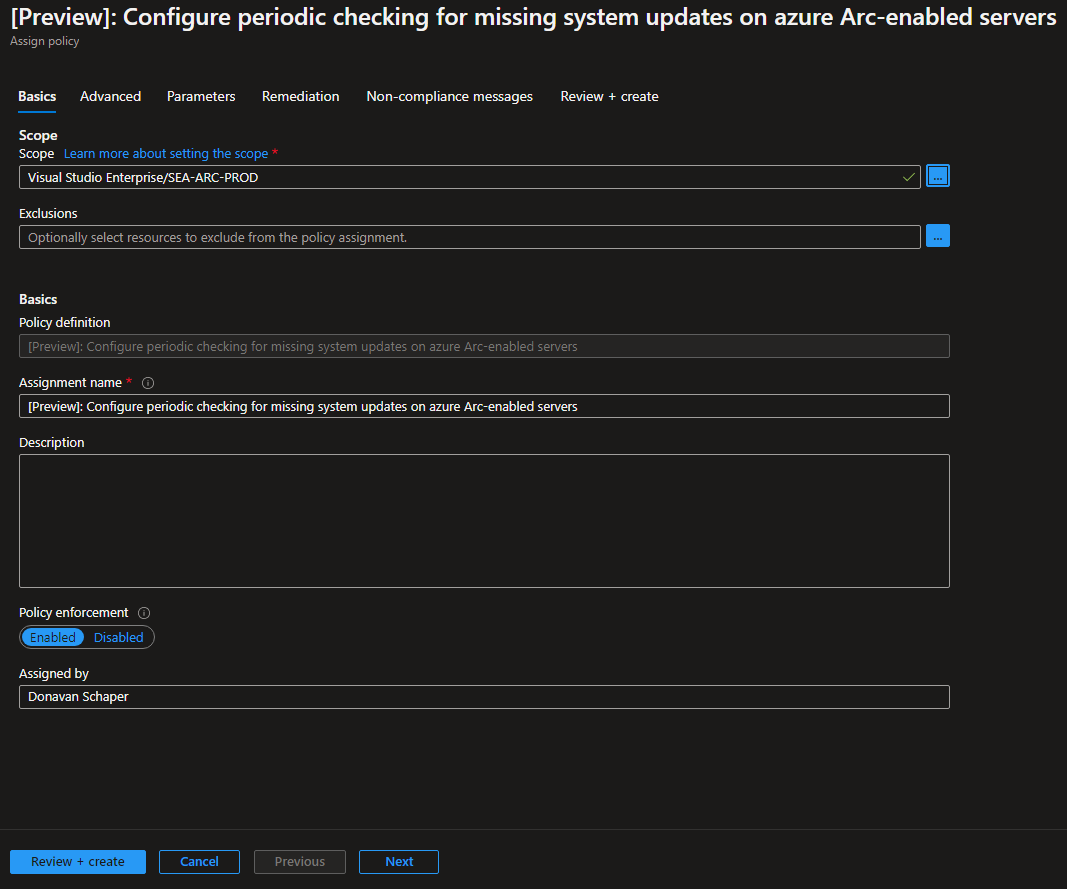
Edit the scope to match your requirements, here we are limiting to the Resource Group containing the Azure Arc servers previously onboarded.
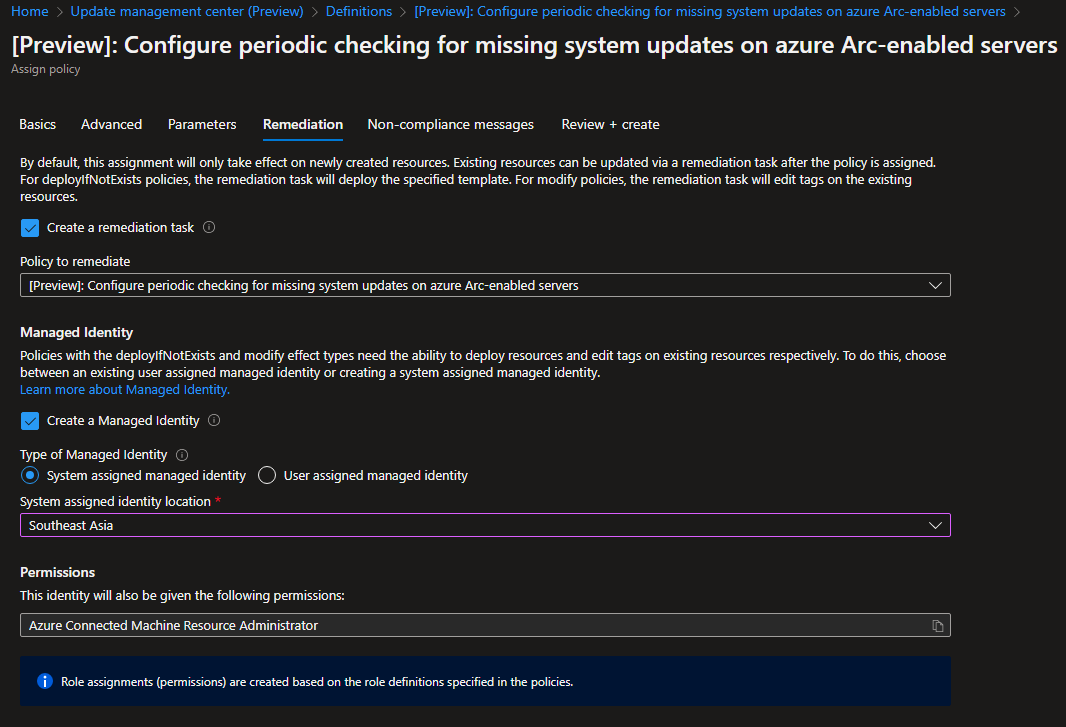
The Policy Assignment wizard will appear and here we can configure the detailed parameters for the policy:
Navigate to the Remediation tab within the wizard, here we can assign a previously created User Assigned Managed Identity or create a new System Assigned Managed Identity to remediate our devices,
Select your preffered option and the region to create the identity in:
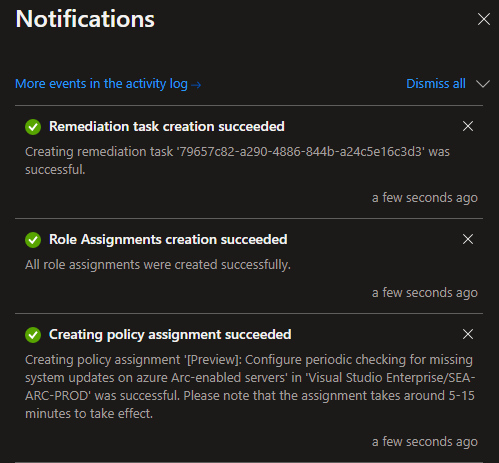
You will notice three items within your ARM Deployment after you select create, namely the Policy Assignment, The Role Assignment and the Remediation Task:
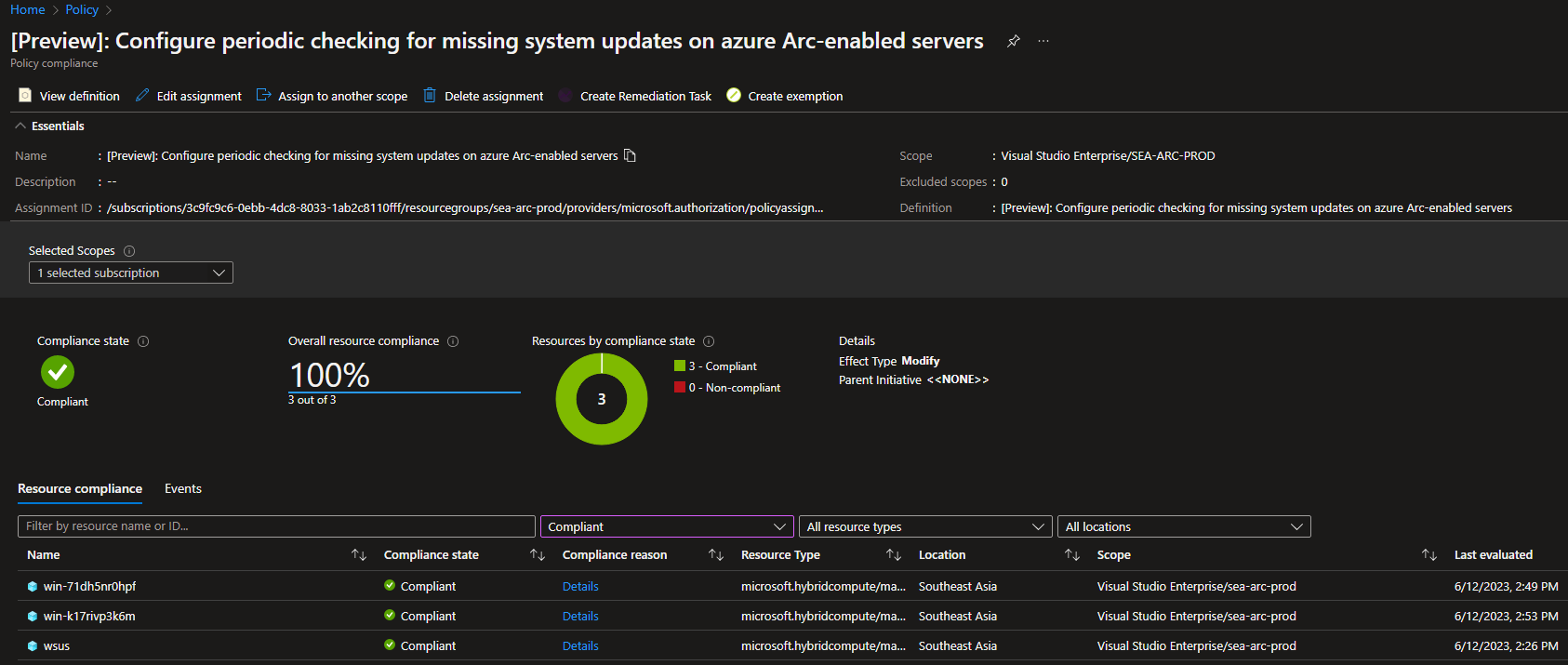
Now navigate back to Azure policy and select the related policy to see it’s compliant status.
Below you can see all your currently onboarded Azure Arc devices adhere to the policy and are marked as fully compliant!
In the next post we will focus on the deployment of patches to our newly configured Azure Arc devices!
View Part 2 of our Azure Arc Update Management Series!